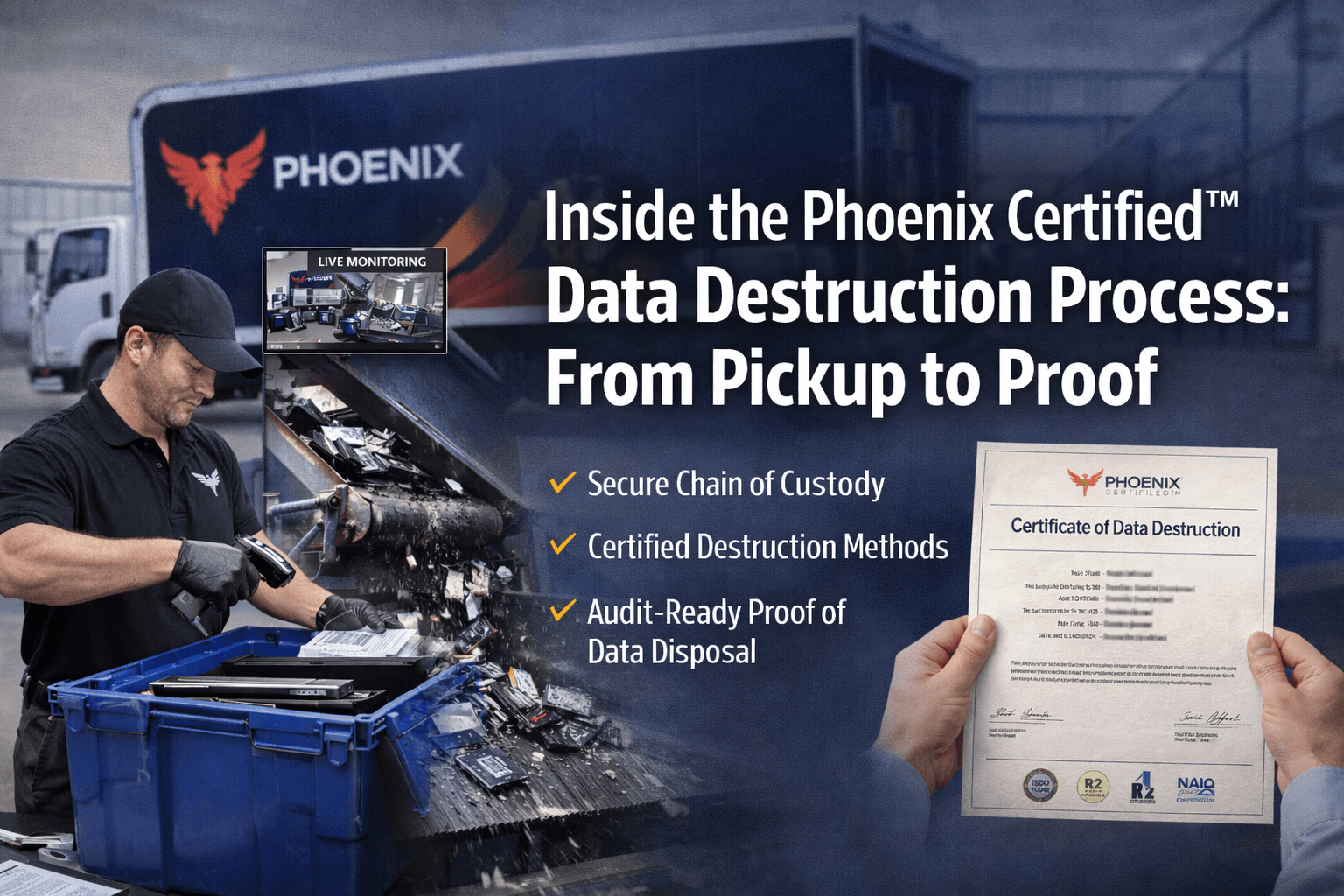
In today’s regulatory climate, data destruction is no longer a simple back-end IT task — it’s a high-risk compliance function. Every retired hard drive, SSD, server, laptop, and backup tape contains potentially sensitive data. If improperly handled, those devices can become a gateway to data breaches, regulatory fines, litigation, and reputational damage.
That’s why organizations are demanding more than just “shredding.” They want transparency. They want chain of custody. They want documentation. They want proof.
This is where the Phoenix Certified™ Data Destruction Process sets a new standard — delivering a fully documented, auditable, and secure pathway from equipment pickup to final destruction verification.
In this blog, we’ll walk step-by-step through what makes the Phoenix Certified™ process different, how it protects your organization, and why “proof” matters just as much as destruction.
Why Certified Data Destruction Matters More Than Ever
Before we dive into the process, it’s important to understand the stakes.
Modern organizations must comply with a growing list of data protection regulations, including:
- HIPAA (healthcare)
- FACTA (financial services)
- GLBA
- PCI-DSS
- State privacy laws
- Contractual data security obligations
- Internal audit requirements
Regulators and auditors aren’t satisfied with verbal assurances. They expect:
- Documented chain of custody
- Controlled handling procedures
- Secure transportation
- Verified destruction methods
- Serialized reporting
- Audit-ready certificates
If any link in that chain breaks, your organization assumes the liability.
The Phoenix Certified™ approach was designed to eliminate those weak links.
Step 1: Secure Scheduling & Pre-Destruction Planning
The Phoenix Certified™ process begins before equipment ever leaves your facility.
What Happens at This Stage?
- Inventory coordination (if applicable)
- Scope definition (hard drives, SSDs, servers, tapes, etc.)
- Risk assessment based on device types
- Secure pickup scheduling
- Chain of custody documentation preparation
This phase ensures:
- No surprises at pickup
- Clear accountability
- Proper documentation from the outset
Many vendors treat pickup as a logistical event. Phoenix Certified™ treats it as the beginning of a documented security process.
Step 2: Controlled Pickup & Documented Chain of Custody
When destruction day arrives, the Phoenix Certified™ team follows strict chain-of-custody protocols.
Key Security Controls Include:
- Trained and vetted personnel
- Serialized collection containers
- Locked transport bins
- Tamper-evident seals
- Signed chain-of-custody documentation
- Time-stamped transfer records
At this point, liability transfers are clearly documented.
This matters because most data loss incidents happen during transportation — not destruction.
Phoenix Certified™ eliminates ambiguity about:
- Who handled the devices
- When custody transferred
- How the equipment was secured
- Where it was transported
Every step is documented and auditable.
Step 3: Secure Transportation to a Certified Facility
Transportation is one of the most overlooked risks in data destruction.
The Phoenix Certified™ process ensures:
- GPS-tracked vehicles
- Secured cargo areas
- Restricted access to materials
- Direct routing to certified processing facilities
There are no unscheduled stops. No third-party handoffs. No warehouse staging without documentation.
Organizations often underestimate this phase — but auditors don’t.
Step 4: Intake Verification & Asset Reconciliation
Upon arrival at the certified facility, every item goes through a controlled intake process.
Intake Includes:
- Verification of seals
- Asset count confirmation
- Serial number scanning (if required)
- Cross-referencing pickup documentation
- Intake logging into secure tracking systems
This is where many providers fail.
Some vendors:
- Batch process without verification
- Skip serial tracking
- Provide generic certificates
Phoenix Certified™ instead focuses on traceability.
If an auditor asks:
“Can you prove this specific drive was destroyed?”
You can.
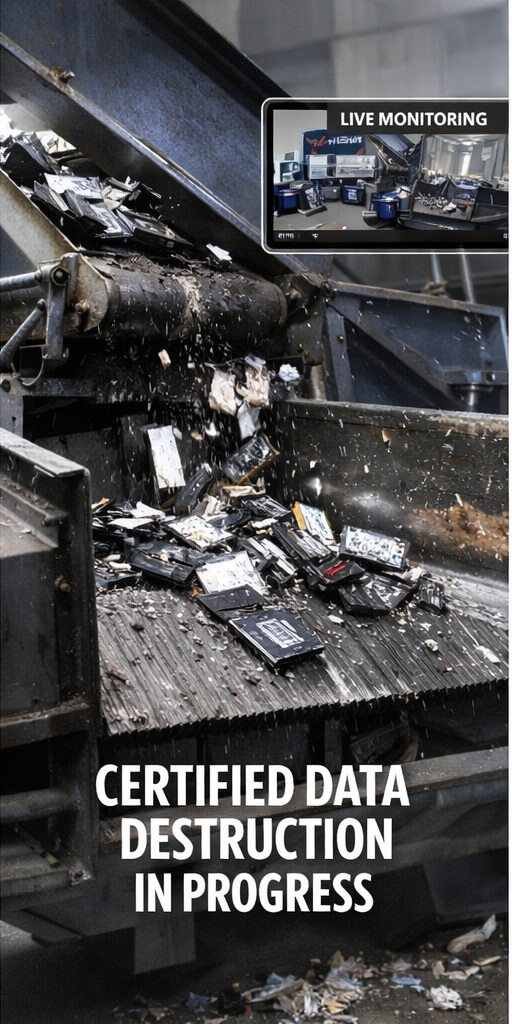
Step 5: Data Destruction Execution (Physical & Logical)
Now comes the destruction phase — but even here, process matters.
Depending on client requirements, Phoenix Certified™ may use:
Physical Destruction
- Industrial shredding
- Crushing
- Disintegration
Logical Data Sanitization
- NIST-compliant overwriting
- Multi-pass wiping
- Verification scans
Destruction methods align with:
- NIST 800-88 guidelines
- Client industry requirements
- Regulatory standards
Not all destruction methods are equal. For example:
- Degaussing alone may not work on SSDs
- Software wiping may not satisfy high-security environments
- Improper shredding particle sizes may fail compliance audits
Phoenix Certified™ selects the correct method for the device type — not just the cheapest method.
Step 6: Witnessed Destruction (Optional but Powerful)
Some organizations — especially in healthcare, finance, defense, and government — require witnessed destruction.
Phoenix Certified™ can provide:
- On-site shredding
- Scheduled facility witnessing
- Video documentation
- Photo documentation
Witnessed destruction provides immediate verification, which can be invaluable during regulatory audits or internal investigations.
Step 7: Downstream Environmental Processing
Data destruction doesn’t end with shredding.
After destruction:
- Materials are sorted
- Recyclables are separated
- Hazardous materials are processed responsibly
- Components are sent to certified downstream vendors
Responsible IT Asset Disposition (ITAD) ensures:
- No illegal exporting
- No landfill dumping
- Environmental compliance
Modern organizations care about sustainability — and regulators increasingly do too.
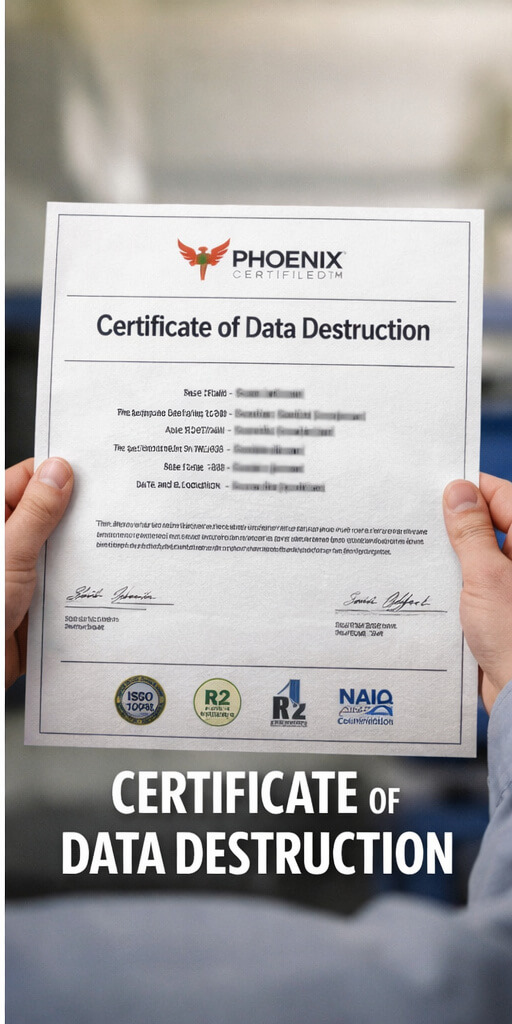
Step 8: Certificate of Destruction (The “Proof” Phase)
This is the stage that separates standard shredding vendors from Phoenix Certified™.
Every Phoenix Certified™ project concludes with a detailed Certificate of Destruction that may include:
- Date of destruction
- Method of destruction
- Device type
- Serial numbers (if required)
- Quantity confirmation
- Authorized signatures
- Facility information
- Regulatory compliance references
This documentation serves as:
- Audit defense
- Legal protection
- Internal compliance verification
- Risk mitigation evidence
Without this documentation, destruction is just an assumption.
With it, it becomes proof.
What Makes Phoenix Certified™ Different?
Let’s summarize the distinguishing factors:
1. Full Chain-of-Custody Documentation
From pickup to final processing.
2. Device-Level Traceability
Not batch destruction.
3. Regulatory Alignment
NIST-compliant methods and industry-specific requirements.
4. Audit-Ready Reporting
Serialized, detailed certificates.
5. Transportation Controls
Often the weakest link — strengthened here.
6. Environmental Responsibility
Secure AND sustainable.
The Risk of Non-Certified Destruction
Organizations that use uncertified or loosely controlled destruction services face serious risks:
- Missing documentation
- No serial-level tracking
- Weak chain of custody
- Incomplete certificates
- Inadequate destruction methods
- Exposure during audits
If a breach occurs and regulators ask for proof — and you can’t produce it — liability increases dramatically.
The cost of proper certified destruction is minimal compared to:
- Breach notification costs
- Legal settlements
- Regulatory fines
- Reputation damage
From Pickup to Proof: Why the Full Process Matters
The phrase “From Pickup to Proof” is intentional.
Destruction isn’t a single event — it’s a documented chain.
Each stage must be:
- Controlled
- Verified
- Recorded
- Auditable
If any link fails, the entire process weakens.
Phoenix Certified™ was designed to:
- Eliminate gaps
- Remove ambiguity
- Provide verifiable accountability
Who Benefits Most from Phoenix Certified™?
The process is especially valuable for:
- Healthcare organizations
- Financial institutions
- Government agencies
- Defense contractors
- Educational institutions
- Enterprise corporations
- Organizations undergoing audits
- Companies preparing for mergers or acquisitions
Any organization handling sensitive data should demand certified, documented destruction.
Preparing for Your Next Data Destruction Event
If you’re planning a device retirement project, consider asking your current provider:
- Can you provide serialized chain-of-custody documentation?
- Are your transportation vehicles tracked and secured?
- Do you follow NIST 800-88 guidelines?
- Can you provide detailed certificates?
- What happens to materials after shredding?
- Can I witness destruction?
- Are your staff vetted and trained?
If the answers are vague — that’s a red flag.
Final Thoughts: Security Is in the Process
True security doesn’t happen at the shredder alone.
It happens:
- At scheduling
- At pickup
- During transport
- At intake
- During destruction
- In documentation
- In reporting
Phoenix Certified™ transforms data destruction from a simple service into a documented compliance solution.
Because in today’s regulatory environment, it’s not enough to destroy data.
You must prove it.