In today’s fast-paced digital economy, organizations are constantly upgrading their IT infrastructure to stay competitive. From laptops and servers to networking equipment and mobile devices, technology cycles are shorter than ever. But what happens to these assets when they reach the end of their useful life? For many organizations, the answer has traditionally been simple disposal. However, that approach is rapidly becoming outdated.
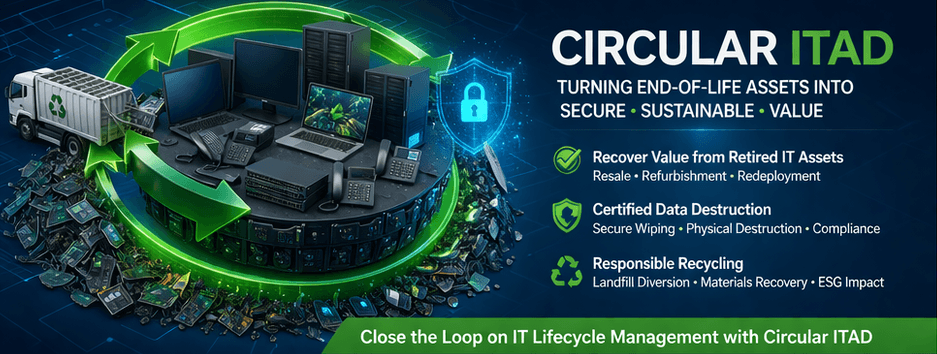
Enter Circular IT Asset Disposition (ITAD), a modern strategy that transforms end-of-life IT assets into opportunities for value creation, sustainability, and enhanced data security. Rather than treating retired equipment as waste, circular ITAD embraces a lifecycle approach that prioritizes reuse, refurbishment, recycling, and responsible data destruction. This shift is not only environmentally responsible but also financially and operationally beneficial.
This blog explores how circular ITAD works, why it matters, and how organizations can leverage it to turn old technology into secure, sustainable value.
What Is Circular ITAD?
Circular ITAD is rooted in the principles of the circular economy, a system designed to eliminate waste and maximize resource efficiency. In a circular model, products and materials are kept in use for as long as possible through reuse, repair, refurbishment, and recycling.
Applied to IT assets, this means:
- Extending the lifecycle of devices through resale or redeployment
- Recovering valuable materials through responsible recycling
- Ensuring secure data destruction at every stage
- Reducing environmental impact while maintaining compliance
Traditional IT disposal follows a linear model: purchase, use, discard. Circular ITAD replaces this with a loop where assets are continuously repurposed or responsibly processed.
The Growing Importance of Circular ITAD
1. Rising E-Waste Concerns
Electronic waste is one of the fastest-growing waste streams globally. Millions of tons of IT equipment are discarded each year, often ending up in landfills or being improperly handled. This contributes to environmental pollution and the loss of valuable materials such as gold, copper, and rare earth elements.
Circular ITAD directly addresses this issue by diverting equipment from landfills and ensuring that materials are recovered and reused whenever possible.
2. Increasing Data Security Risks
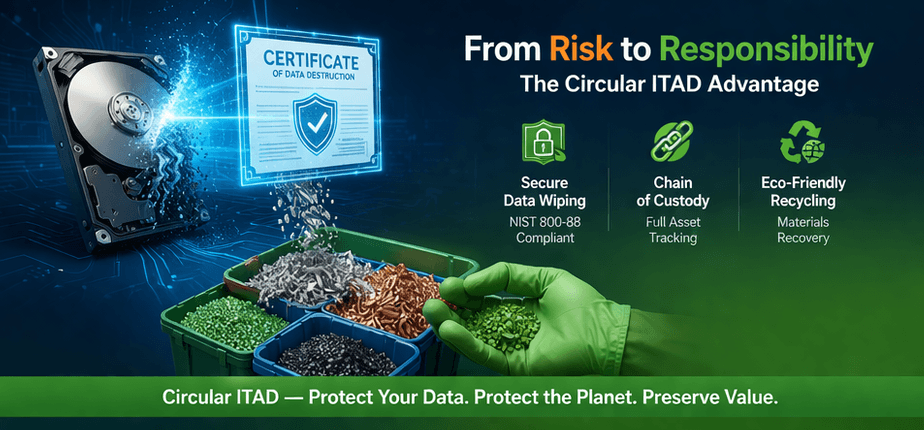
One of the most critical concerns with retired IT assets is data security. Hard drives, SSDs, and other storage devices often contain sensitive information, including customer data, financial records, and proprietary business information.
Improper disposal can lead to data breaches, regulatory fines, and reputational damage. Circular ITAD integrates certified data destruction processes into every step, ensuring that data is securely erased or destroyed before any reuse or recycling occurs.
3. Regulatory and Compliance Pressures
Organizations must comply with a growing number of regulations related to data protection and environmental responsibility. These may include:
- Data privacy laws
- Industry-specific compliance requirements
- Environmental regulations governing e-waste disposal
Circular ITAD providers help organizations meet these requirements through documented processes, certifications, and audit-ready reporting.
The Core Pillars of Circular ITAD
1. Asset Recovery and Value Maximization
Not all retired IT assets are obsolete. Many devices still retain significant market value, especially if they are only a few years old. Circular ITAD focuses on:
- Testing and grading equipment
- Refurbishing devices for resale
- Redeploying assets internally
By recovering value from these assets, organizations can offset the cost of new technology investments.
2. Secure Data Destruction
Data security remains the foundation of any ITAD strategy. Circular ITAD ensures that:
- All data-bearing devices are identified and tracked
- Certified wiping or physical destruction methods are used
- Detailed certificates of destruction are provided
This guarantees that sensitive information is permanently removed before assets leave organizational control.
3. Responsible Recycling
For equipment that cannot be reused, recycling is the next step. Circular ITAD providers use environmentally responsible processes to:
- Recover valuable materials
- Safely handle hazardous components
- Minimize environmental impact
This ensures compliance with environmental standards while contributing to resource conservation.
4. Chain of Custody and Transparency
A critical component of circular ITAD is maintaining a secure and transparent chain of custody. This involves:
- Tracking assets from pickup to final disposition
- Providing detailed reporting and documentation
- Ensuring accountability at every stage
Transparency builds trust and ensures that organizations can confidently demonstrate compliance during audits.
Business Benefits of Circular ITAD
Cost Savings and Revenue Generation
Circular ITAD transforms a cost center into a potential revenue stream. By reselling or refurbishing equipment, organizations can recover value that would otherwise be lost.
Additionally, reducing disposal costs and avoiding regulatory penalties contributes to overall financial efficiency.
Enhanced Brand Reputation
Sustainability is no longer optional. Customers, investors, and stakeholders increasingly expect organizations to demonstrate environmental responsibility.
Implementing a circular ITAD strategy signals a commitment to sustainability, which can enhance brand reputation and strengthen stakeholder relationships.
Improved Risk Management
By integrating secure data destruction and compliance-focused processes, circular ITAD reduces the risk of:
- Data breaches
- Legal liabilities
- Environmental violations
This proactive approach to risk management protects both the organization and its customers.
Support for ESG Goals
Environmental, Social, and Governance (ESG) initiatives are becoming central to corporate strategy. Circular ITAD directly supports ESG objectives by:
- Reducing carbon footprint
- Promoting responsible resource use
- Ensuring ethical handling of electronic waste
Key Components of a Successful Circular ITAD Program
1. Partnering with a Certified ITAD Provider
Choosing the right ITAD partner is critical. Look for providers with certifications such as:
- R2v3 (Responsible Recycling)
- ISO standards for quality, environmental, and information security management
These certifications ensure that the provider follows best practices in data security and environmental responsibility.
2. Implementing Asset Tracking Systems
Effective asset tracking ensures that every device is accounted for throughout its lifecycle. This includes:
- Inventory management
- Barcode or RFID tracking
- Real-time reporting
Accurate tracking reduces the risk of asset loss and improves accountability.
3. Establishing Clear Policies and Procedures
Organizations should develop internal policies for IT asset disposition that include:
- Data sanitization requirements
- Approval processes for asset disposal
- Documentation and reporting standards
Clear guidelines ensure consistency and compliance across the organization.
4. Educating Employees
Employees play a key role in the success of circular ITAD. Training programs should focus on:
- Proper handling of retired equipment
- Data security best practices
- Sustainability goals
An informed workforce helps prevent mistakes and supports organizational objectives.
Overcoming Common Challenges
Balancing Security and Sustainability
One of the biggest challenges is ensuring that sustainability efforts do not compromise data security. Circular ITAD addresses this by prioritizing secure data destruction before any reuse or recycling.
Managing Logistics
Handling large volumes of IT assets across multiple locations can be complex. Partnering with an experienced ITAD provider simplifies logistics through coordinated pickups, centralized processing, and streamlined workflows.
Measuring Impact
Organizations may struggle to quantify the benefits of circular ITAD. Metrics such as:
- Revenue recovered from asset resale
- Reduction in e-waste
- Carbon footprint savings
can help demonstrate the value of the program.
The Future of IT Asset Disposition
As technology continues to evolve, the importance of circular ITAD will only grow. Several trends are shaping the future of the industry:
Increased Automation
Advanced technologies such as AI and automation are improving the efficiency of asset tracking, data destruction, and refurbishment processes.
Greater Emphasis on Sustainability
Organizations are placing greater emphasis on sustainability, driving demand for circular ITAD solutions that align with environmental goals.
Stricter Regulations
Governments and regulatory bodies are introducing stricter requirements for data protection and e-waste management, making compliance a top priority.
Integration with IT Lifecycle Management
Circular ITAD is becoming an integral part of broader IT lifecycle management strategies, ensuring that sustainability and security are considered from procurement to disposal.
Why Circular ITAD Is a Strategic Advantage
Circular ITAD is no longer just a disposal strategy. It is a strategic advantage that enables organizations to:
- Unlock hidden value in retired assets
- Strengthen data security and compliance
- Reduce environmental impact
- Enhance brand reputation
By adopting a circular approach, organizations can turn what was once considered waste into a powerful driver of value and sustainability.
Final Thoughts
The transition from linear disposal to circular ITAD represents a fundamental shift in how organizations manage their technology assets. It is a move toward a more responsible, efficient, and secure future.
In a world where data breaches are costly, regulations are tightening, and sustainability is a priority, circular ITAD offers a comprehensive solution that addresses all three challenges.
Organizations that embrace this approach will not only reduce risk and improve efficiency but also position themselves as leaders in sustainability and innovation.
The question is no longer whether to adopt circular ITAD, but how quickly you can implement it to start realizing its benefits.