In today’s digital-first business environment, organizations are generating and retiring IT assets at an unprecedented pace. From servers and networking equipment to employee laptops and mobile devices, the lifecycle of technology is shrinking while regulatory scrutiny is intensifying. As a result, IT Asset Disposition (ITAD) is no longer just an operational afterthought—it has become a critical component of cybersecurity, compliance, sustainability, and corporate governance.
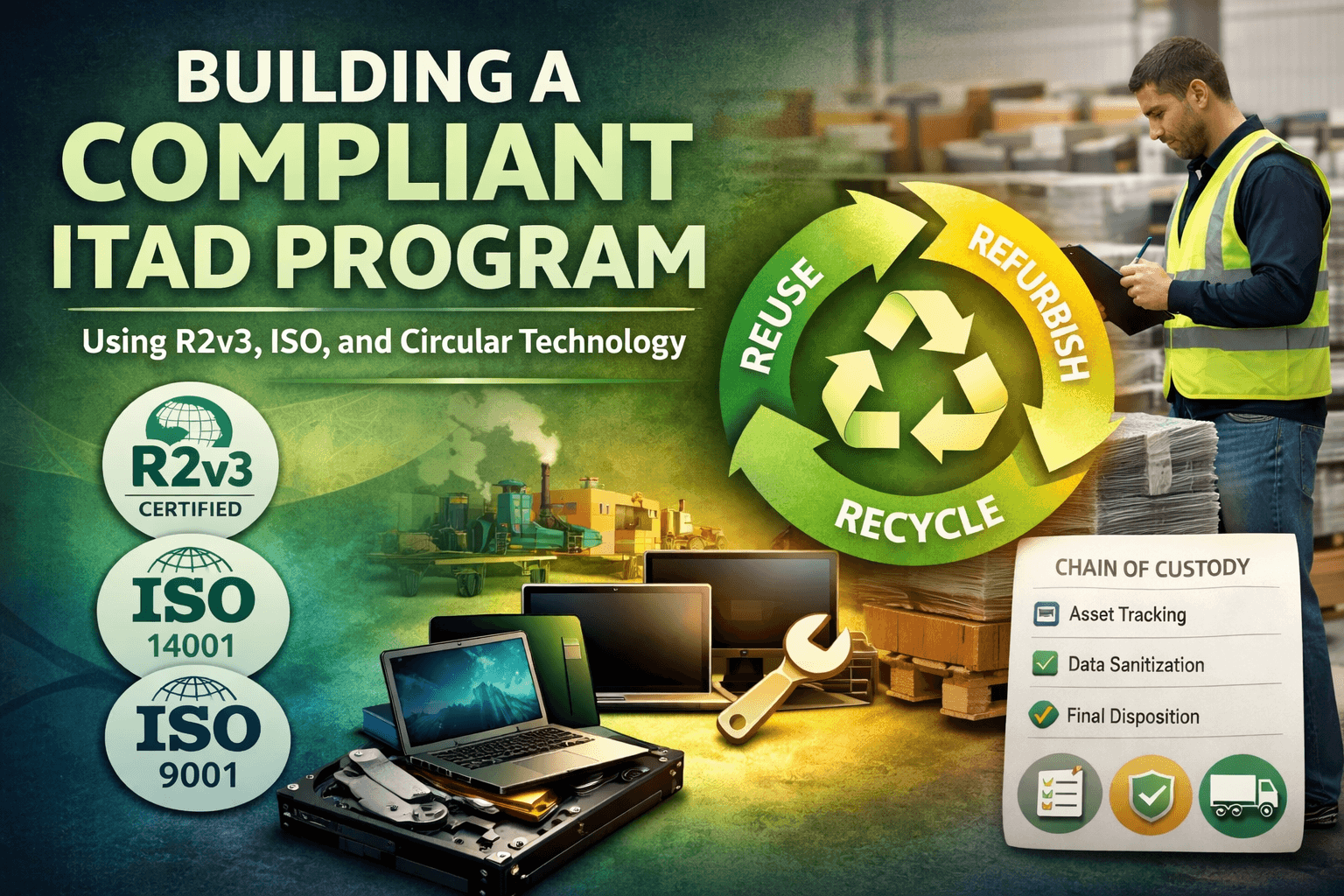
Building a compliant ITAD program requires more than simply recycling old equipment. It demands a structured, auditable, and secure approach grounded in globally recognized standards such as R2v3 and ISO frameworks, while also embracing circular technology principles that maximize value recovery and environmental responsibility.
This blog explores how organizations can design and implement a robust ITAD program that aligns with R2v3 certification, ISO standards, and circular economy strategies—ensuring compliance, reducing risk, and unlocking measurable business value.
Why ITAD Compliance Matters More Than Ever
Organizations today face a convergence of risks when disposing of IT assets:
- Data security risks from improper data destruction
- Regulatory risks tied to environmental and privacy laws
- Financial risks from underutilized asset recovery
- Reputational risks linked to improper e-waste handling
Improper IT disposal can result in data breaches, fines, and public backlash. At the same time, businesses are under increasing pressure to meet ESG (Environmental, Social, Governance) goals and demonstrate sustainable practices.
A compliant ITAD program addresses all of these concerns by creating a standardized, transparent, and defensible process for managing end-of-life IT assets.
Understanding R2v3: The Foundation of Responsible ITAD
R2v3 (Responsible Recycling version 3) is one of the most widely recognized global standards for electronics recycling and IT asset disposition. It provides a structured framework for ensuring environmental responsibility, data security, and operational transparency.
Key Components of R2v3
- Data Sanitization Requirements
R2v3 mandates strict protocols for data destruction, including documentation and verification of sanitization methods. - Downstream Vendor Accountability
Organizations must track where materials go after processing, ensuring no illegal dumping or unethical recycling practices. - Environmental Protection Standards
Proper handling of hazardous materials is required to prevent environmental harm. - Chain of Custody Documentation
Every asset must be tracked from pickup through final disposition, creating a fully auditable trail.
Why R2v3 Matters
R2v3 is not just about recycling—it’s about accountability. It ensures that every step of the ITAD process is documented, secure, and compliant with global best practices. For organizations, partnering with an R2v3-certified provider—or aligning internal processes with R2v3 principles—significantly reduces risk.
Leveraging ISO Standards for ITAD Excellence
While R2v3 focuses specifically on electronics recycling and ITAD, ISO standards provide broader frameworks for quality, environmental management, and occupational safety.
Key ISO Standards for ITAD Programs
ISO 9001: Quality Management Systems
ISO 9001 ensures that ITAD processes are consistent, repeatable, and continuously improving. It emphasizes:
- Process standardization
- Documentation and recordkeeping
- Customer satisfaction and performance tracking
In ITAD, this translates to reliable workflows, reduced errors, and improved audit readiness.
ISO 14001: Environmental Management Systems
ISO 14001 focuses on minimizing environmental impact. Within ITAD, it supports:
- Responsible recycling practices
- Waste reduction strategies
- Compliance with environmental regulations
This standard aligns closely with sustainability goals and ESG reporting.
ISO 45001: Occupational Health and Safety
ISO 45001 ensures safe working conditions for employees involved in IT asset handling and processing. This includes:
- Safe dismantling procedures
- Hazardous material handling
- Workplace risk assessments
The Power of ISO Integration
When combined, these ISO standards create a comprehensive management system that supports:
- Operational efficiency
- Regulatory compliance
- Continuous improvement
- Risk mitigation
For ITAD programs, ISO frameworks provide the operational backbone that complements R2v3’s specialized requirements.
The Role of Circular Technology in ITAD
Traditional IT disposal models often focus on destruction and recycling. However, circular technology introduces a more strategic approach—prioritizing reuse, refurbishment, and value recovery before recycling.
What Is Circular Technology?
Circular technology is based on the principles of the circular economy, where products and materials are kept in use for as long as possible. Instead of a “take-make-dispose” model, organizations adopt a “reuse-repurpose-recycle” strategy.
Benefits of Circular ITAD
1. Maximized Asset Value
Refurbishing and reselling IT equipment can generate significant financial returns compared to immediate destruction.
2. Reduced Environmental Impact
Extending the lifecycle of devices reduces e-waste and lowers carbon emissions associated with manufacturing new equipment.
3. Stronger ESG Performance
Circular IT practices directly support sustainability initiatives and reporting requirements.
4. Improved Resource Efficiency
Organizations extract more value from existing assets rather than continuously investing in new hardware.
Building a Compliant ITAD Program: Step-by-Step
Creating a compliant ITAD program requires a structured approach that integrates R2v3, ISO standards, and circular principles.
Step 1: Conduct an IT Asset Inventory and Risk Assessment
Start by identifying all IT assets within your organization and assessing:
- Data sensitivity levels
- Asset lifecycle stages
- Potential compliance risks
This step establishes the foundation for decision-making and prioritization.
Step 2: Define Clear ITAD Policies and Procedures
Develop formal policies that outline:
- Data destruction requirements
- Asset handling procedures
- Vendor selection criteria
- Documentation standards
These policies should align with R2v3 and ISO frameworks to ensure consistency and compliance.
Step 3: Implement Secure Data Destruction Protocols
Data security is the most critical aspect of ITAD. Ensure that:
- All data-bearing devices are sanitized using certified methods
- Processes are documented and verified
- Certificates of destruction are issued
This step protects against data breaches and regulatory violations.
Step 4: Establish Chain of Custody Controls
Track every asset from the moment it leaves your facility to its final disposition. This includes:
- Serialized asset tracking
- Transportation logs
- Processing documentation
A strong chain of custody is essential for audits and compliance verification.
Step 5: Select Certified ITAD Partners
If outsourcing ITAD, choose providers that are:
- R2v3 certified
- ISO 9001, 14001, and 45001 certified
- Transparent in their processes
Vendor selection is one of the most critical decisions in building a compliant program.
Step 6: Integrate Circular Technology Practices
Before recycling or destroying assets, evaluate opportunities for:
- Reuse within the organization
- Refurbishment and resale
- Donation programs
This step enhances both financial returns and sustainability outcomes.
Step 7: Maintain Documentation and Audit Readiness
Compliance requires thorough documentation, including:
- Asset inventories
- Chain of custody records
- Data destruction certificates
- Vendor certifications
Regular internal audits ensure that processes remain aligned with standards.
Step 8: Continuously Improve the Program
Leverage ISO frameworks to implement continuous improvement practices:
- Monitor performance metrics
- Identify process gaps
- Update policies as regulations evolve
A compliant ITAD program is not static—it must adapt to changing risks and requirements.
Common ITAD Compliance Gaps to Avoid
Even well-intentioned organizations can fall short if they overlook key areas.
Lack of Documentation
Without proper records, compliance cannot be proven—even if processes are followed correctly.
Inadequate Vendor Oversight
Failing to vet downstream vendors can expose organizations to environmental and legal risks.
Over-Reliance on Destruction
Destroying all assets may seem secure, but it eliminates opportunities for value recovery and sustainability gains.
Weak Chain of Custody
Gaps in tracking can lead to lost assets, data exposure, and audit failures.
Measuring the Success of Your ITAD Program
To ensure your program is delivering value, track key performance indicators (KPIs):
- Percentage of assets reused or resold
- Revenue generated from asset recovery
- Compliance audit pass rates
- Data destruction verification rates
- Reduction in e-waste
These metrics provide insight into both operational efficiency and strategic impact.
The Business Case for a Compliant ITAD Program
Investing in a structured ITAD program delivers measurable benefits:
Risk Reduction
Minimizes the likelihood of data breaches, regulatory fines, and reputational damage.
Cost Optimization
Generates revenue through asset recovery and reduces disposal costs.
ESG Alignment
Supports sustainability goals and enhances corporate responsibility initiatives.
Operational Efficiency
Streamlines processes and improves asset lifecycle management.
Future Trends in ITAD Compliance
As technology and regulations evolve, ITAD programs must adapt.
Increased Regulatory Oversight
Governments are implementing stricter e-waste and data privacy laws, requiring more rigorous compliance.
Greater Emphasis on ESG Reporting
Organizations will need to demonstrate measurable sustainability outcomes tied to ITAD practices.
Advanced Data Destruction Technologies
Innovations in data sanitization will enhance security and efficiency.
Expansion of Circular Economy Models
Businesses will increasingly prioritize reuse and refurbishment over disposal.
Conclusion
Building a compliant ITAD program is no longer optional—it is a strategic necessity. By integrating R2v3 standards, ISO frameworks, and circular technology principles, organizations can create a program that not only meets regulatory requirements but also delivers financial, operational, and environmental benefits.
A well-designed ITAD program protects sensitive data, ensures regulatory compliance, reduces environmental impact, and unlocks hidden value within retired IT assets. As the digital landscape continues to evolve, organizations that invest in compliant and sustainable ITAD practices will be better positioned to manage risk, drive efficiency, and lead in corporate responsibility.
Ultimately, ITAD is not just about disposing of old equipment—it is about building a smarter, safer, and more sustainable future for technology management.