In today’s data-driven economy, organizations face mounting pressure to securely manage and dispose of end-of-life IT assets. From laptops and servers to mobile devices and storage media, every piece of hardware contains sensitive information that—if improperly handled—can expose a business to serious financial, legal, and reputational risks.
For years, companies have relied on traditional data destruction methods such as shredding, wiping, or degaussing. While these methods still play a role, a new, more advanced standard is emerging: Phoenix Certified™ data destruction.
But what exactly is Phoenix Certified™, and how does it differ from traditional approaches? More importantly, which option is right for your organization?
This guide breaks down the key differences, benefits, risks, and strategic considerations so you can make an informed decision.
Understanding Traditional Data Destruction
Traditional data destruction refers to the established methods used to eliminate data from storage devices. These methods generally fall into three categories:
1. Physical Destruction
This includes:
- Shredding hard drives
- Crushing devices
- Incineration
Pros:
- Immediate and irreversible
- Visually verifiable
- Effective for highly sensitive data
Cons:
- Eliminates any chance of asset value recovery
- Generates e-waste
- Requires strict chain-of-custody controls
2. Data Wiping (Logical Destruction)
This method overwrites data using software to ensure it cannot be recovered.
Pros:
- Preserves hardware for resale or reuse
- Environmentally friendly
- Cost-efficient
Cons:
- Requires verification and auditing
- Risk of incomplete erasure if not properly executed
- Dependent on software standards and operator accuracy
3. Degaussing
A process that uses strong magnetic fields to disrupt data on magnetic storage devices.
Pros:
- Fast and effective for certain media types
- Eliminates data without physical destruction
Cons:
- Limited to magnetic media (e.g., HDDs, tapes)
- Renders devices unusable
- Cannot be used on SSDs or flash storage
The Limitations of Traditional Methods
While traditional data destruction methods are widely accepted, they come with significant limitations in today’s regulatory and cybersecurity landscape:
Lack of Standardization
Not all vendors follow the same protocols. This inconsistency can lead to gaps in compliance and security.
Limited Transparency
Organizations often rely on certificates of destruction without full visibility into how the process was executed.
Chain-of-Custody Risks
If devices are mishandled at any stage—from pickup to destruction—data can be exposed.
Compliance Challenges
With regulations like HIPAA, GDPR, and CCPA, businesses must demonstrate not just destruction, but documented proof of secure handling.
Environmental Concerns
Physical destruction contributes to e-waste and undermines sustainability initiatives.
What Is Phoenix Certified™ Data Destruction?
Phoenix Certified™ represents a modern, standardized, and auditable approach to data destruction. It goes beyond simply “destroying data” and focuses on security, transparency, compliance, and sustainability throughout the entire IT asset disposition (ITAD) lifecycle.
Rather than being a single method, Phoenix Certified™ is a comprehensive framework that integrates:
- Verified data sanitization processes
- Strict chain-of-custody controls
- Real-time tracking and reporting
- Compliance with industry standards (R2v3, NIST, ISO, etc.)
- Emphasis on reuse and value recovery when possible
Think of it as the difference between a basic service and a certified, end-to-end system of accountability.
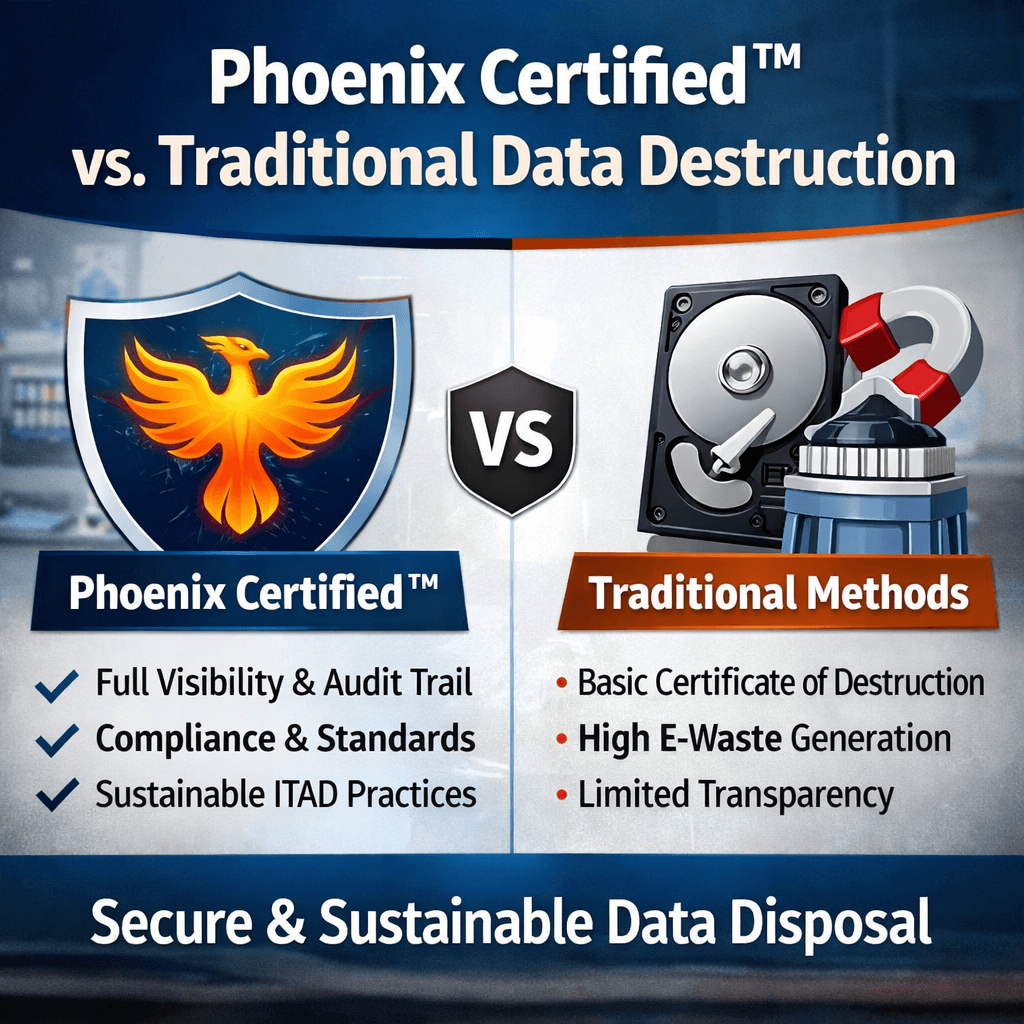
Key Differences: Phoenix Certified™ vs Traditional Data Destruction
1. Approach: Process vs. Outcome
Traditional:
- Focuses on the end result (data is destroyed)
- Limited attention to how the process is managed
Phoenix Certified™:
- Focuses on the entire lifecycle
- Ensures every step—from pickup to final disposition—is documented and verified
👉 Why it matters: Regulators and auditors increasingly require proof of process, not just outcome.
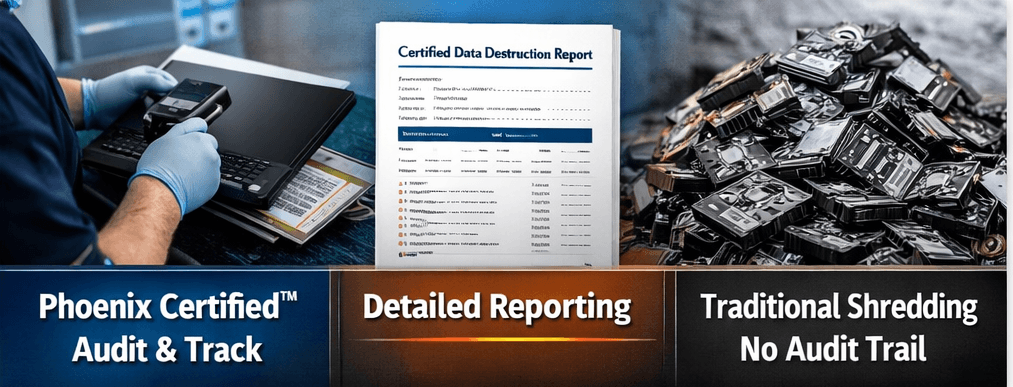
2. Transparency and Reporting
Traditional:
- Provides a certificate of destruction
- Minimal detail about execution
Phoenix Certified™:
- Offers detailed audit trails
- Real-time tracking of assets
- Serialized reporting for each device
👉 Why it matters: In the event of a data breach or audit, detailed documentation can protect your organization.
3. Chain of Custody
Traditional:
- May rely on manual tracking
- Increased risk of human error
Phoenix Certified™:
- Implements secure logistics protocols
- Uses tracking systems to monitor assets at every stage
- Ensures accountability from pickup to final processing
👉 Why it matters: Most data breaches during disposal occur due to breakdowns in chain of custody—not the destruction method itself.
4. Compliance and Standards Alignment
Traditional:
- May or may not align with recognized standards
- Compliance often depends on vendor practices
Phoenix Certified™:
- Built around industry frameworks such as:
- NIST 800-88 (data sanitization)
- R2v3 (responsible recycling)
- ISO 27001 (information security)
👉 Why it matters: Compliance is no longer optional—it’s a legal requirement in many industries.
5. Data Security Assurance
Traditional:
- Security depends on execution quality
- Limited verification mechanisms
Phoenix Certified™:
- Requires validation and verification of data destruction
- Incorporates quality control checks
- Uses certified processes and technologies
👉 Why it matters: “Trust but verify” is critical in data security.
6. Sustainability and Asset Value Recovery
Traditional:
- Often defaults to shredding
- Results in lost asset value and increased e-waste
Phoenix Certified™:
- Prioritizes reuse and resale when secure
- Reduces environmental impact
- Supports ESG (Environmental, Social, Governance) goals
👉 Why it matters: Sustainable IT practices are becoming a competitive and regulatory expectation.
7. Risk Management
Traditional:
- Reactive approach
- Limited documentation in case of incidents
Phoenix Certified™:
- Proactive risk mitigation
- Comprehensive documentation for legal protection
- Reduced exposure to fines and reputational damage
👉 Why it matters: The cost of a data breach far exceeds the cost of proper data destruction.
Real-World Scenario Comparison
Scenario 1: Traditional Approach
A company sends 500 retired laptops to a vendor for shredding.
- Devices are picked up and transported
- A certificate of destruction is issued
- No detailed tracking per device
- Limited insight into handling process
Risk:
If even a few devices are lost or mishandled, the company may have no way to trace the issue.
Scenario 2: Phoenix Certified™ Approach
The same company uses a Phoenix Certified™ provider.
- Each device is logged and serialized at pickup
- Chain-of-custody is tracked in real time
- Data is securely wiped or destroyed based on policy
- Detailed reports are generated for each asset
- Audit-ready documentation is provided
Outcome:
Full visibility, reduced risk, and compliance assurance.
When Should You Choose Traditional Data Destruction?
Traditional methods may still be appropriate in certain situations:
- Highly sensitive data requiring immediate destruction
- Legacy systems where reuse is not feasible
- Emergency disposal scenarios
However, even in these cases, organizations should ensure:
- Vendor credibility
- Proper documentation
- Compliance with standards
When Is Phoenix Certified™ the Better Choice?
Phoenix Certified™ is ideal for organizations that:
- Handle regulated data (healthcare, finance, government)
- Require audit-ready documentation
- Have sustainability goals
- Want to maximize asset value recovery
- Need full visibility into ITAD processes
The Future of Data Destruction
The shift toward frameworks like Phoenix Certified™ reflects a broader trend:
Data destruction is no longer just an IT task—it’s a strategic business function.
Organizations are being held accountable not only for protecting data during its use, but also for how it is handled at the end of its lifecycle.
Key trends shaping the future include:
- Increased regulatory scrutiny
- Demand for transparency and traceability
- Integration of ITAD into cybersecurity strategies
- Emphasis on sustainability and circular economy practices
Final Thoughts
Choosing between Phoenix Certified™ and traditional data destruction is not just about selecting a method—it’s about choosing a level of security, accountability, and strategic alignment.
Traditional methods can still serve a purpose, especially in high-security scenarios requiring immediate physical destruction. However, they often fall short in today’s environment where compliance, transparency, and sustainability are critical.
Phoenix Certified™, on the other hand, represents a next-generation approach—one that transforms data destruction from a basic service into a comprehensive, auditable, and value-driven process.
If your organization is looking to reduce risk, improve compliance, and align with modern best practices, Phoenix Certified™ is not just an upgrade—it’s a necessity.